When it comes to network security, our industry has been lucky to have flown under the radar for so long. Unfortunately, cybercrime is becoming a growth industry; recent security breaches have brought new attention to smart home and IoT devices, and the old method of security through obscurity is no longer a viable option. Having worked as an integrator, and more recently alongside integrators providing tools to support their networks, security is at the top of my mind. But as an industry, security best practices are neglected when it comes to securing client networks and systems as evidenced by recent attacks.

Image: Thinkstock
Some of the largest attacks were not very technical and accessed more than 100,000 IP cameras to leverage a combination of known credentials and publically accessibility. The targeted devices had known or default usernames and passwords and were accessible on the public internet or not properly secured behind a firewall. This botnet attack was devastating to the internet and generated an obscene amount of traffic (1.2Tbps), which brought the targeted servers to a screeching halt. These attacks likely used some cameras and NVRs installed by many of you reading this article. Why was this equipment chosen as the way in? Many of the camera manufacturers are original equipment manufacturers (OEM) for many other brands, which include some who sell to our industry, and the practice of port forwarding to enable remote access for customers is all too common in our systems.
Stop Port Forwarding
In the CEDIA networking classes that I teach and through my company, Ihiji, I have been saying for years that port forwarding is a practice that needs to stop. Control systems manufacturers, such as Control4, also have issued official statements to their dealers warning them against the practices of port forwarding. Port forwards essentially poke a hole in your firewall, which leaves that device publically accessible on the internet. That is kind of like sitting on a street corner in Manhattan with a lap full of five dollar bills, passing out for a nice long nap, and then waking up expecting to still have all of your money. It’s a dangerous practice with severe consequences. Many of the devices integrators install are general purpose computers, which means that once someone has access to that device on your local network, they can use that as a bridge to access other devices on that local area network that aren’t exposed via a port forward. It’s essentially a big, unlocked back door into your client’s network.
That’s scary stuff! So why does the industry still use the practice of port forwarding if it is such a security risk? Surprisingly, there are some manufacturers who still recommend port forwarding to allow integrators and direct customers remote access to their equipment. That puts everyone in a vulnerable position. Any manufacturer that is still using port forwarding as their primary means of remote access should train dealers on alternative methods or develop other methods of remote access. There are also legitimate ways to mitigate risk when port forwarding. For example, if you are running an internal virtual private network (VPN) service, it will often require a port forward to a secure service and port. If you are port forwarding for services such as VPN, you should be sure to keep your firmware and security patches current.
Port forwarding can be used as a temporary means of remote access when other methods are not working, like when troubleshooting a tough tech support problem on a device installed in someone’s home. In this case, it is best to use an obscure external port, rather than a common port such as 22. It is also highly recommended that you have a secure username and password on that device, it has up-to-date firmware to reduce the risk of exploitation and that you maintain the active port forward for the minimum time required.
Use VPNs Responsibly
Now that we know the risks of a port forward, what are the alternatives? VPN technology is commonly used for remote access. It allows a remote tunnel to be established to a network, which gives a user access to the devices on that network almost as if they were sitting on-site. VPN is frequently used for technicians, network administrators and programmers to remotely connect to a client site. These remote connections can be used to troubleshoot and resolve support issues or make systems changes such as programming or configuration updates. It is very convenient for the business, employee, and client because it doesn’t require an on-site visit.
VPN is a very powerful tool, but with great power comes great responsibility. If you are using VPN for remote access, you should be very certain that you are using a protocol that supports encryption. Without encryption, the information you are sending over that remote tunnel could be intercepted in clear text, which leaves usernames and passwords exposed to anyone who might be snooping. This is most common when you are on public Wi-Fi networks at coffee shops, airports, restaurants, etc. If you are using a protocol such as PPTP without encryption for your client VPN connections and someone is sniffing out traffic, there is a chance that they could intercept the remote IP address of the VPN server, the username, and password. With this information, they could replicate the connection, and at that point, they have full access to your client’s networks.
It gets worse if your clients are then connecting to their cameras or NVRs using an insecure protocol like telnet or HTTP. The attacker could also intercept that information to gain access to those devices. Or if a business uses a common username and password to all of their client’s systems, a practice that is also too common, then anyone who gets ahold of those credentials has now potentially gained access to multiple networks. A good best practice for VPN is to use truly unique credentials for each remote network, ensure those credentials are managed securely and to restrict access to that information to only those who need remote access. It is also common to put in place remote access policies that state who has access to the VPN, in what cases it can be used and how each use should be logged for auditing.
A more common method of remote access is to use cloud services. A classic industry example of cloud services is Panamax Bluebolt, which gives a technician or homeowner the ability to remotely reboot a power unit through an app or website without the need for a port forward or VPN. Another broader example is Nest cameras, which give camera access to a client’s IP camera without a port forward or VPN.
The Advantage of Tunneling Tools
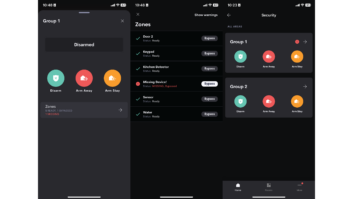
An increasingly more common method for technicians to remotely access a client site for troubleshooting or configuration changes are tunneling tools within Ihiji, Ovrc, Bakpak, etc. These tools allow for better user management, permissions, and auditing. Using the tunneling feature, a technician can accomplish many of their common remote support tasks without the need for full VPN access or port forwarding. Many of these tools log each tunnel session so that you can see which technicians access each device and at what time. The central user management allows a service manager or business owner to easily disable remote access or remove a technician if there is a change in responsibilities or employment status. That is more scalable for a small business that is juggling hundreds to thousands of remote clients and need to support them on a daily basis.
Finally, take some time to invest in training and education. Port forwarding, VPN, and remote access are only a small piece of the security conversation. Security is a cat and mouse game, so there are always new best practices, policies, and exploits to be aware of. Many manufacturers offer free training at industry distributors, trade shows and online. CEDIA offers excellent training opportunities at the annual trade show and also during Integrated Systems Europe (ISE). CEDIA EST423 Remote Access and Troubleshooting and CEDIA EST463 Advanced Networking Security are two CEDIA courses are being offered at the show in San Diego this September.
It is time this dirty little secret of port forwarding and remote access be discussed publically and addressed. Hopefully, I’ll see you at the educational seminars that CEDIA is putting together to navigate this hot trend. Until then, the Consumer Technology Association recently released a security checklist that you can download for free. You can also request a copy of the Ihiji white paper “10 Best Practices to Make Your Client Networks More Secure” by emailing [email protected].
Michael Maniscalco is VP of product for Ihiji.