As the threat of ransomware has reached new heights in 2021, residential systems businesses across the globe are doubling-down on their defense against the scourge — making sure they’ve done everything they can to avoid their clients and themselves from becoming a victim.
Even the smallest of residential systems businesses are prime targets for hackers, who see small businesses as generally easy to penetrate and plunder. Moreover, many of these businesses also realize they need to stay up to speed on the latest tricks of ransomware hackers, given that their customers are depending on them to stand between their homes and all the hackers looking to compromise all the Internet-of-Things devices installed in their smart homes.
Says Glen Merlin Johnson, founder of Adaptive Design Group, a smart home systems integrator specializing in smart home lighting: “It is our responsibly as tech designers and specifiers to ensure that our clients are not only physically protected in their homes by intruders, but also safe from cyber intrusions on all of our integrated wired and wireless electronics.”

David Henry, a general manager a Netgear — maker of Netgear Armor cybersecurity software for the home, agrees: “With the explosion of connected devices in the home — from baby monitors to smart TVs — all of which can be compromised, we understand how overwhelming it can be for individuals and families to know what to do to keep themselves and their information safe.
“We realized that a new type of security solution was needed. And with this version of Netgear Armor, we take worry out of the equation by providing a comprehensive ‘set-it-and-forget-it’ service.”
Indeed, successful ransomware attacks across the U.S. have proven so troublesome this year, they’ve triggered an executive order from President Joe Biden — nudging all U.S. businesses to get serious about ransomware protection.
Says Biden: The order “calls for federal agencies to work more closely with the private sector to share information, strengthen cybersecurity practices, and deploy technologies that increase reliance against cyberattacks.
“It outlines innovative ways the government will drive to deliver security and software — using federal buying power to jumpstart the market and improve the products that all Americans use.”
During 2021 alone, businesses across the U.S. have been reeling from successful ransomware attacks, including attacks against SolarWinds, a commonly used IT management software program; the ransomware disruption of service on the Colonial Pipeline, the largest conduit of refined oil products in the U.S.; and the ransomware seizure of computer files of the Washington DC Metropolitan Police Department.
Still other ransomware takedowns include a takeover of computer files at goliath meatpacking concern JBS Foods as well as at the National Basketball Association.
Granted, authorities have occasionally gotten lucky against ransomware hackers during 2021. Excellent cyber forensic work by the U.S. Department of Justice, for example, clawed back $2.3 million in Bitcoin that the Colonial Pipeline paid to ransomware hackers to help get its computer network up-and running again.
Says Lisa O. Monaco, U.S. Deputy Attorney General: “Following the money remains one of the most basic, yet powerful tools we have. We will continue to target the entire ransomware ecosystem to disrupt and deter these attacks. Today’s announcements also demonstrate the value of early notification to law enforcement. We thank Colonial Pipeline for quickly notifying the FBI when they learned that they were targeted by Dark Side.”
Ransomware By the Numbers
Even so, hackers get away with their exploits more often than not, extorting hundreds of thousands of businesses across the globe each year — and disrupting the day-to-day operations of each.
Overall, 37 percent of organizations across the globe have experienced some sort of ransomware attack between May 2020 and April 2021, according to a study from cybersecurity firm Sophos, “The State of Ransomware 2021.”
Based on that survey of 5400 IT managers at mid-sized organizations across 30 countries, the study also found that the average ransom paid to recover data from a ransomware attack was $170,404.
Not surprisingly, many of the criminals behind those successful ransomware attacks kissed-off promises to restore computer files once ransoms were paid, according to the study.
Specifically, on average, victimized organizations in the study that paid ransoms only got back 65 percent of their data. Only 8 percent of organizations forking over money to hackers were able to retrieve all of their files, according to the Sophos study.

Equally vexing for the victim organizations was the cost to day-to-day business. On average, the average cost to restore the impact of a successful ransomware attack on a mid-size business — taking into account downtime, lost wages, device cost, network cost, lost sales, and ransomware paid, was $185 million.
Plus, hackers have increasingly exploited a new wrinkle in their ransomware schemes during the past year — threatening, and often making good on threats, to publish sensitive data found in business files on the Dark Web if a victim business refuses to pay a ransom.
Granted, smaller residential systems businesses hit by ransomware are most likely going to see a much smaller impact on their bottom line than what is being experienced at mid-level and enterprise-sized competitors. But even with the smallest residential systems business, a ransomware shutdown is going to hurt, grind business to a halt, and run the owner ragged trying to find a way to get computers up-and-running again.
Moreover, even though a homeowner customer hit with ransomware probably won’t blame his/her systems installer, many may look at the CI business that installed all their smart home devices and say, “Why didn’t you at least warn me?”
Software to the Rescue
Fortunately, residential systems businesses looking to protect themselves and customers have a raft of new software available specifically designed to thwart ransomware attacks. Here is a representative sampling of that software, all highly rated and all available at entry-level prices. Essentially, your computer security personnel can try-out these programs at extremely low rates, and, in some cases, opt to bring-in an enterprise-level alternative to the same program should you deem it necessary.
Plus, should you decide that one or more of these programs truly delivers on its promises, you can recommend and install the program for residential customers who are also looking to safeguard their network from ransomware intrusion:
- Bitdefender Antivirus Plus: Starts at $23.99/year. A player in the anti-ransomware space for a number of years now, Bitdefender Plus offers many of layers of anti-ransomware protection, along with a myriad of other security features. The software is designed to eliminate on-the-spot known ransomware. Plus, it will also watch for unexpected behaviors on your PC or network that indicate ransomware activity — such as a sudden, wholesale change in the names of files or the extension names of files. Essentially, Bitdefender backs up all your files at the first whiff of what it determines may be a ransomware attack beginning to deploy, and then restores the files after the attack has been fully neutralized.
- ZoneAlarm by Checkpoint: $39.95/year. This is another highly rated anti-ransomware package that erases all vestiges of ransomware on your computer system once detected. It also embeds “bait” files on your computer network, designed to lure ransomware into changing those files first and setting off alarms that enable ZoneAlarm to neutralize the attack before it spreads to actual company files. Plus, ZoneAlarm can repair files after a ransomware attack, if possible.
- Kaspersky Security Cloud — Free: Free. It’s hard to argue with free, so if you’re looking for instant peace-of-mind today, Kaspersky Security Cloud — Free may be your ticket. Kaspersky is designed to protect against two types of ransomware: one that encrypts your files, making them unusable to you, and ransomware that encrypts your entire hard disk, making the entire computing device unusable. Kaspersky can also neutralize ransomware that locks up your computer screen. And it offers monitoring and auto-neutralization of typical ransomware behaviors — like wholesale renaming of files and/or file extensions. Other features include Idle Scan, which monitors resources like system memory when you’re not using your computer. And there’s a rootkit scan function, which helps betray ransomware activity designed to elude typical monitoring of Windows and typical monitoring used by everyday anti-virus software.
- Sophos Home Premium: Starts at $44.99/year. This program is a lite version of a more robust version of anti-ransomware protection that Sophos offers to enterprise-level businesses. Sophos is designed to plug known security holes in commonly used software. Plus, it offers download reputation analysis on programs that you’re thinking of downloading that may have a bad reputation. Sophos could do the trick for a small business that decides enterprise-level protection is not necessary — especially since this lite version enables you to remotely safeguard, monitor, and manage the software on up to ten remote computers. One caveat: Novice users may face a bit of a learning curve before they can use Sophos’ advanced features.
- NeuShield Data Sentinel: Starts at $23.99/year. Neushield is the only candidate in this pack that does not offer ransomware protection. Instead, Neushield is an after-the-fact ransomware product that offers one-click restoration of files encrypted by ransomware, if possible. Essentially, Neushield is not a panacea against a ransomware attack, but giving it a whirl after your business has been taken down by ransomware is well worth the price of entry. Users install Neushield on their computers before an attack occurs, which enables the software to “virtualize” any changes to the files on your system. Theoretically, virtualized files cannot be corrupted by a ransomware attack, given that they are not fully operational files in a virtualized state. Users of Neushield regularly decide when to approve changes in virtualized files, which make those files operational once again. It’s a powerful way to put a buffer on any files in your system that undergo changes — including changes ransomware is seeking to make to your files.
Joe Dysart is an internet speaker and business consultant based in Manhattan. Web: www.dysartnewsfeatures.com.
Cybersecurity at CEDIA Expo
guardDog was turning heads and winning checks at CEDIA Expo (for the latter, the $5000 TechStarter Award) with its Cybersecurity-as-a-Service offering.
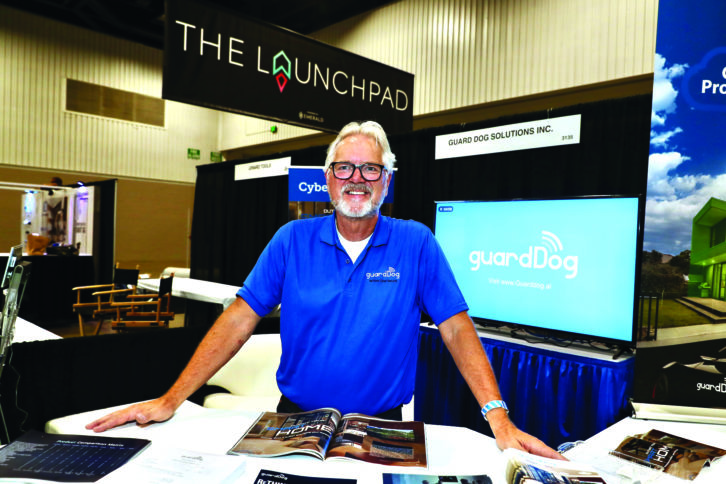
The guardDog Protective Cloud Services (PCS) is an AI-powered network security solution that doesn’t require the dealer to have cybersecurity expertise to operate. The only piece of hardware involved is a simple box named Fido that plugs into the client’s router.
Once activated, the Fido device goes to work by detecting threats and vulnerabilities on the network. From there, a cloud dashboard displays incidents by threat level and shows information on how to resolve the issues before they become a problem. The dealer can fix the problem themselves, or he or she could choose to sub-contract it to a different cybersecurity service (guardDog maintains that they detect the problems before they become issues, but do not fix them).
guardDog has several dealer-friendly plans available. Learn more at https://guarddog.ai.