In previous issues we discussed hardware and software methods for preventing anonymous and unauthorized access. Regrettably, no matter how many fortress walls are built or gates erected, there is a very simple way to subvert most security systems. Unfortunately, it’s often you, your co-workers, and your clients who are the weakest link. The power of simple conversation can destroy the most complex password procedures, methodologies, and barbed wired firewalls.
Pride and Prejudice
“Social engineering” is the method of hacking a system (any system really) by convincing folks to provide access, or information on how to access it. The victim does not know that they have been duped by an imposter presenting themselves as a family member, friend, or business associate.
This method of entry relies on our inherent human nature of stereotyping and trust in our own ability to not be conned. These two human preoccupations of presumption and saving face present an ample “theater stage” on which a talented conversationalist can play.
The Babington Plot
Infiltration by imposters is a method that has been used since shortly after humans organized themselves into factions and tribes. One classic example is the arrest and killing of Mary Queen of Scots.
Mary, cousin to the queen, had a rightful claim on the throne, But, in the politics of that time, Queen Elizabeth imprisoned Mary, who was forbidden any communication with the outside world. A plan was concocted to deliver encrypted messages via her weekly delivery of beverages.
While the messages were soon discovered, the agents of Elizabeth could not break the code. Mary was caught in a plot to assassinate Elizabeth when a main associate discussed facts of the communication with an conspirator. The agents used the simple technique of praising Mary’s associates’ intelligence and craft (and a desire to overthrow the current queen). By bostering Mary’s associates’ confidence and pride and by using uncovered names to prove his legitimacy, the code key was obtained.
Mary was implicated in the plot and summarily beheaded.
The False Authority Syndrome
We all have pictures in our heads of what a “hacker” looks like. Movies and books by William Gibson have given us a multitude of images to reinforce the notion that these folks always appear as either bespectacled geeks or skateboarding “alternative types” wearing hoodies. The truth, of course, is that the people who work to infiltrate our networks are, well, people. More often than not, the presentation offered fits within our expectations of how a network support person, audiovisual tech, or supervisor will look and act.
Once we are convinced by the supposed authority of the individual or individuals, we often over inform in an attempt to be helpful. This is where the trap is sprung, although we only know of this after it is too late to recover.
Phone Fakery
In person, an individual attempting to gain information for access can be exposed by a chance overlap with real company technicians, documented by security systems, or by unconscious facial reactions. Talented hucksters may be able to pull off this dangerous version of an improv game, but the risks are much higher when attempting in person.
Contacting victims remotely provides a bit of stealth while enabling the ability to connect with multiple parties from one location—using a phone call to present oneself as the manager of a tech team, cable TV dispatch, or even a work associate. The technique of mixing stern bluster and direct requests with savvy name dropping will often result in people lowering their guard.
Phishing Food
Then there is the infamous Risotto Recipe. This unique take on crafting the perfect Italian creamy rice dish was obtained by a classic phishing technique of a campaign manager during the recent elections.
How was the recipe, along with campaign strategies, obtained? The campaign manager clicked a link in an email from someone pretending to be the IT manager for the organization. The link brought him to a page with a seemingly legitimate URL, which loaded a malware.
We are all familiar with the more notorious attempts to get us to click on links in emails to win a free iPad or share in the millions of a ousted prince. Most of us know enough to avoid these, and email tools have become smarter in identifying them. Trouble often occurs, however, when we receive such emails from what appears to be a trusted source. Often, the email address is spoofed or sent with a note stating, “This is my personal email, my work one is down.” We or our clients may not question it because it came our organization or a staff member name that they know.
Foil the Falsifiers
So now that we understand some of the concepts and techniques of the social engineering hackers, just how can we protect our clients and ourselves?
The mantra here is the same as with the other methods we use to secure a network: limit and manage. Just like we use a managed switch or firewall to limit the type of data and the origination points, so too can we limit from whom to accept requests.
Your staff and clients may be barraged by multiple requests that can cause confusion and allow an interloper to sneak inside all the noise. Make sure your clients know exactly whom their contact is; there should only be one or two individuals from the company that contact the client. Make sure the staff knows the hierarchy and procedure for scheduling with the client.
Educate your clients on the fact that no staff person will ask you for passwords, Wi-Fi keys, encryption methods, or network layout. This information should be noted and accessed via documentation at the office, not directly from the client.
Never allow unannounced techs to work on a system, unless verified by the approved managers with a list of onsite tech names.
Ensure that any techs who leave your company (by choice or not), be immediately removed from email and remote monitoring software. This includes social tools, where a tech may be a Facebook, Twitter, or Instagram page manager. (Many try to reach out via these to clients who follow your outreach.)
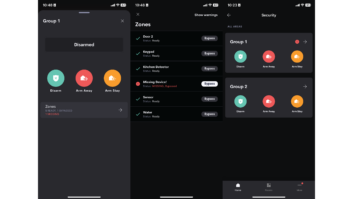
Make sure that any remote system software tools are managed by an admin with the ability to add, remove, and restrict access. This is crucial, as all too often for the sake of expediency, we share a common user/password scheme.
These rules for access and scheduling may seem overwrought, but by being vigilant you can prevent damage to your systems, and more importantly to your client.
Securing a network requires more than hardware and settings, it demands personal vigilance and adherence to rules. When the weakest link is our own innate desire to trust and accommodate, methods to limit personal presumptions must be put in place. Otherwise you only have yourself to blame.