In addition to limiting the type of data delivered, grouping the physical ports into broadcast domains means that we can give each its own IP address set.
The modern home is essentially a data network, and as integrators we are responsible for the safety and stability of the systems that we install. Even if we are not “the network guys” implementing a data network, it is of the utmost urgency that we understand what security has been put into place in our clients’ homes.
Our previous article in this series covered how firewalls can be a first line of defense by segmenting client computers and ports accessible.
[The Gigabit Home: Another Brick in the Firewall]
Network security is about segmentation and control where overlapping layers simultaneously re-enforce and fine-tune preceding management filters.
A switch’s main task is to enable the efficient and steady delivery of data to client computers, keeping busy segments flowing while leaving lesser sections unaffected.
A managed network switch’s ability to control the type of messages forwarded and who gets them makes them a natural security layer. This ability to manage data is also a very handy method of inhibiting access to interlopers.
No system is perfect, and very knowledgeable individuals or tools can eventually find a way in if people and the tools we put in place are not persistently vigilante.
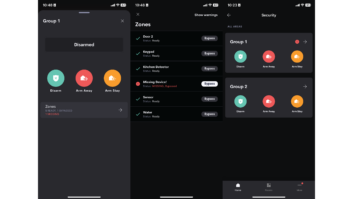
One of the tools that a managed switch provides is the ability to create multiple independent networks spanning off of one “input” connection. This segmentation into broadcast domains gives us Virtual Local Area Networks.
A standard multiport switch can be divided in groups of physical ports. For example, a 16- port switch can be divided into four groups of four ports each—group one set for voice over IP (VoIP), group two for video traffic, group three for the accounting department, and group four for the creative group.
In the switch software tools we assign a name—VLAN 2, VLAN 4 or Accounting, Creative, Media, etc. Each of these segments are independent and cannot (internally) connect to the other without and additional server/router connection.
How does this increase security? In addition to limiting the type of data delivered, grouping the physical ports into broadcast domains means that we can give each its own IP address set. Accounting can be 192.168.2.x, while the media segment can be 192.168.4.x and so on. It is also possible to set the segments to different IP classes.
In effect, we are setting up not only separate isolated nodes but also NATs (Network Address Translation), which are the jumps from one IP address group to another. Just like we discussed when looking into firewalls, this provides an additional hurdle for a hacker to overcome. If the interlopers get into one segment, it does not mean they have ready access to the others.
Network switches can also limit access by restricting the Machine Access Controller (MAC) addresses allowed to connect. The MAC address is a unique address given to any network device chip—each RJ45 and Wi-Fi radio theoretically has its own chip address. (This is an OSI layer 2 address, separate from the layer 2 IP addressing).
Limiting access or blocking specific MAC addresses provides a very discreet level of security. In addition, managed switches have tools to combat a common MAC overflow attack where a breach is created by generating a wave of MAC access requests to the switch.
While a switch does, in some ways, duplicate tools implemented by firewalls, a switch can manage both layer 2 and layer 3 connections. Managing each layer is another net to inhibit intruders.
Adding the rules and tools of a managed switch in addition to a firewall is time consuming, requires a specialized technician, and is labor intensive. It also means more time is required to add new devices or provide service access (like a new streaming app.)
Implementing such a network also requires vigilance. As an installer, it also means maintaining the system by being attentive to system alerts and educating your client on how their actions impact security.
Compared to the hassle of a client being compromised, services stolen, and trust shattered, the work of securing a network is no big deal.