Network security is a balancing act where the needs of clients on a network and the bandwidth required are weighed against providing protection from nefarious actors. By utilizing the multilayered capabilities of firewalls, managed switches, and wireless techniques, we can provide our clients with an architecture that is robust and secure.
Setting up barriers is effective but somewhat passive, once things are set up. To really stay on top of a network’s health, we need something akin to a real-time reporting.
Within many Ethernet devices is a way of monitoring network operations to provide preemptive notification of issues and performance optimization.
Logging Reports
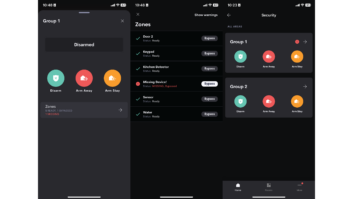
Logging is a ubiquitous part of control systems. Many systems log everything that is sent or received, while others only note when errors occur. With programming, we can use our code to note and store when and for how long entry points (doors, windows, garage, etc.) are opened or if lights are on in an unoccupied room and for how long. In this way, we can verify and log activities for immediate action or future reference.
We have devices logging activities all around us. The most ubiquitous is electrical usage. We all have the simple meter outside our residence showing to anyone with access just how much electricity we use. Electrical and water meters are increasingly tied to wireless transmitters for local agencies to retrieve detailed reports on usage.
[The Gigabit Home: Wireless Network Security Wants and Needs]
Smart thermostats not only learn our daily schedules and adjust temperatures accordingly, but they also can act as mini weather stations. These IoT devices can record the outside temp, sense a home’s occupancy, and track daily HVAC usage. If the home has integrated multi-stage heating and/or zones, the usage is recorded and stored on a webpage for review.
Many of these consumer and even prosumer devices can be accessed with tools such as Perl and Python to collect and collate the reports.
Also, nearly every enterprise-class router and switch provides the ability to log connections, connection attempts, routes, and admin access attempts. These, for the most part, need to be retrieved and formatted to review or present.
Data networks have far more activity, so it only stands to reason that we should be able to log the activity in a more real-time manner.
Management Master
As I’ve described in previous articles, Ethernet and its layered security is about management and control—from the TCP-IP protocol to the use of managed switches and all the parts in between.
Making sure who and what gets through and to whom it gets to is just as important as ensuring that there is ample bandwidth for streaming content. We have to meet the demands of our client needs and make sure that there is no downtime due to a chink in the armor.
[The Gigabit Home: Another Brick in the Firewall]
The majority of switches and firewall settings are of the “set and forget” type; once you establish the rules of network data flow, the units simply run them. A VLAN may need some modification based on a new user or retrofit of a room, but once this is established, there is little to actively monitor.
When issues do arise, the first indication is usually a client complaining of “sluggish” operation or a down system. Would it not be better to have preemptive warnings sent to you as the potential for issues builds?
Simple and Secure
We have all had the moment when our antivirus software suddenly generates a pop-up report stating that it nullified a threat. We, the user, did nothing more than install the software and tell it to keep us safe and informed when action is taken.
In a similar way, we can utilize a simple tool to keep an eye on the network goings on and inform us when things are amiss or exceed a set parameter. Simple Network Management Protocol works within the application layer to monitor, log, and report on the network’s vitals. Using a common language, SNMP can be set to poll statistics such as bandwidth usage, segment traffic, source and destination connections, and more.
SNMP can allow you to set alarms that send out emails or text messages, warning you when any part of the network has an issue or notes an irregularity. You can also use the data to generate reports and graph trends, which is very helpful when trying to deduce an issue or even present reasons for an upgrade.
This simple protocol is available in universally available from within high-end network gear but can be found in lower cost managed switches, as well. The level and size of a network that can be monitored will vary, with free tools handling less and more intensive suites costing a pretty penny.
Logging network devices, operations, and their interactions is not technically a security tool. The tool, at its core, does not place impediments to deter people or software seeking to compromise a system. But, having the ability to review a record and trace where an issue arose is vitally important when dissecting an event.
Notifications, in real time, cannot stop a threat but they can make you and your team aware of an issue before the client knows anything is wrong. Having the ability to be preemptive with your client can go a long way toward minimizing an attack or stopping it before any real damage can be done.